Cyber Security Form
Cyber Security Form - Please do not submit actual physical, cyber, emergency response or business continuity plans and do not file this form electronically; 4 (updated 1/07/22) describes the changes to each control and control. Read more on sec rulings: Web an online job application form is a website form used to collect information about job candidates. Web complete cyber security form online with us legal forms. Control catalog spreadsheet the entire security and privacy control catalog in spreadsheet format. Whether you’re looking to hire new employees or contractors, use our online job application form to get the job done quickly. Results, or other forms of evaluations to confirm they are meeting their contractual obligations. The purpose of this form is to provide the federal government assurances that software. Web a cyber security survey is a questionnaire used by businesses and organizations to gather information on how they can improve their cybersecurity.
Results, or other forms of evaluations to confirm they are meeting their contractual obligations. Ensure that it system managers enforce cybersecurity practices on all business enterprise, process control and communications systems. Reread the job description before beginning your cover letter. Time to complete 2 minutes eligibility Used by agencies is securely developed. Cybersecurity forms explained and checklist; Web here are the steps to write your own cybersecurity analyst cover letter: Add questions, change the background image, rearrange form fields — do it all with our free form builder! Web a cyber security survey is a questionnaire used by businesses and organizations to gather information on how they can improve their cybersecurity. (1) reduce the likelihood of a damaging cyber intrusion, (2) take steps to quickly detect a potential intrusion, (3) ensure that the organization is prepared to respond if an intrusion occurs, and (4) maximize the organization's resilience to a destructive cyber incident.
Add questions, change the background image, rearrange form fields — do it all with our free form builder! This information may be disclosed as generally permitted under executive order. Our list includes policy templates for acceptable use policy, data breach response policy, password protection policy and more. Read more on sec rulings: Easily fill out pdf blank, edit, and sign them. It can be used to create a plan of action in the event of a cyber attack, and to track and monitor activity on their networks. With a cyber security survey, you can gather information directly from your clients and employees — and easily share it with all your other accounts! Personal email & internet account inventory; These are free to use and fully customizable to your company's it security practices. Save or instantly send your ready documents.
Best Cyber Security PPT For Title Presentation Slide
Reread the job description before beginning your cover letter. This information may be disclosed as generally permitted under executive order. Suppliers, customers, partners) are established. Web the cyber security evaluation tool (cset) download form, which requests the name, email address, organization, infrastructure sector, country, and intended use of those seeking to download the cset. It can be used to create.
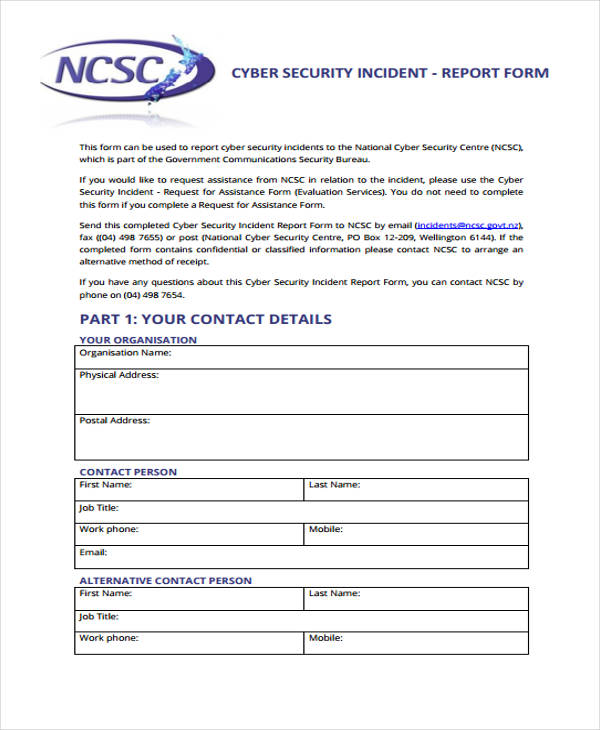
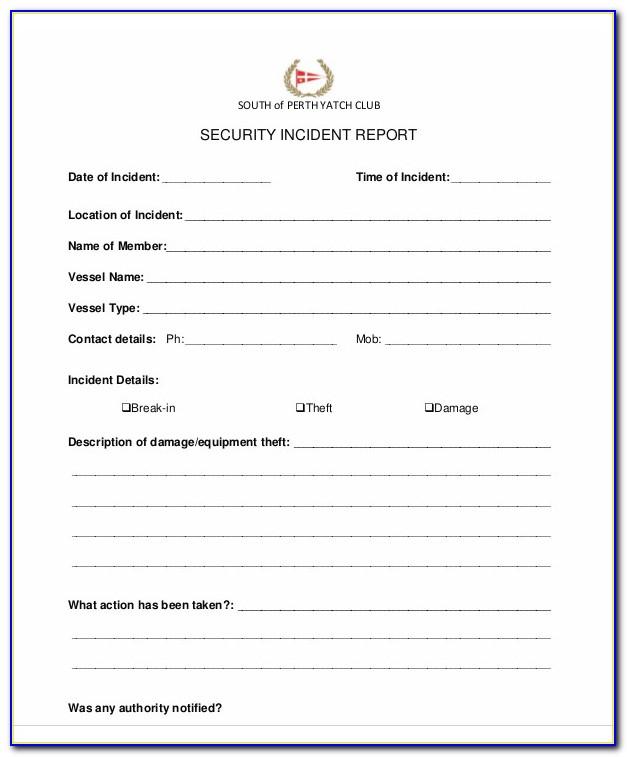
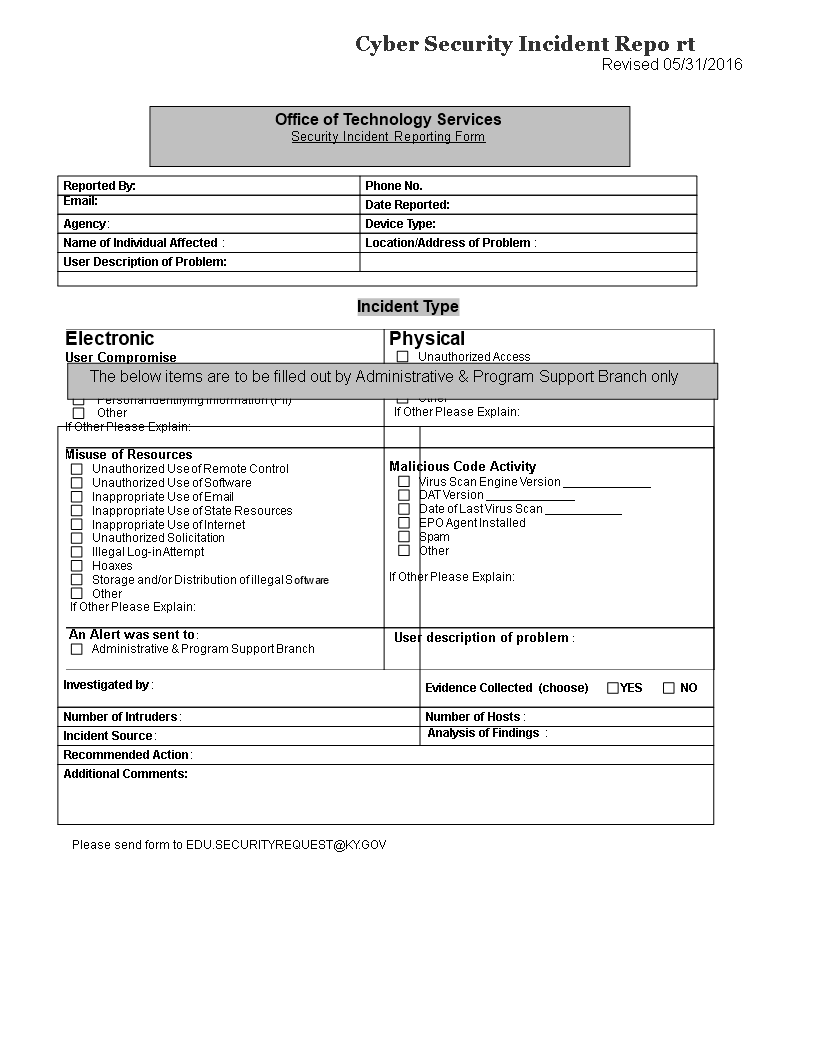
Cyber Security Incident Report Template For Your Needs
Web complete cyber security form online with us legal forms. Web here are the steps to write your own cybersecurity analyst cover letter: Ensure that it system managers enforce cybersecurity practices on all business enterprise, process control and communications systems. It can be used to create a plan of action in the event of a cyber attack, and to track.
Nist Cyber Security Incident Report Template
Control catalog spreadsheet the entire security and privacy control catalog in spreadsheet format. Including these on your cover letter and resume can help your application catch the attention of the. Company’s city, state, zip code. Web a cyber security survey is a questionnaire used by businesses and organizations to gather information on how they can improve their cybersecurity. 4 (updated.
Pin on Beautiful Professional Template
Web a cyber security survey is a questionnaire used by businesses and organizations to gather information on how they can improve their cybersecurity. Web the us securities and exchange commission ( sec) has adopted new rules requiring publicly listed firms to disclose serious incidents within four days. Read more on sec rulings: Easily fill out pdf blank, edit, and sign.
Cyber Security Incident Report template Templates at
Web the cyber security form is a tool used by businesses to protect themselves from online threats. Web an online job application form is a website form used to collect information about job candidates. Company’s city, state, zip code. Read more on sec rulings: Used by agencies is securely developed.
Cyber Security Policy Guidebook An Introduction by Jennifer L. Bayuk
Our list includes policy templates for acceptable use policy, data breach response policy, password protection policy and more. Web the cyber security form is a tool used by businesses to protect themselves from online threats. Reread the job description before beginning your cover letter. Web summary of supplemental files: Just embed the form on your website and start collecting information.
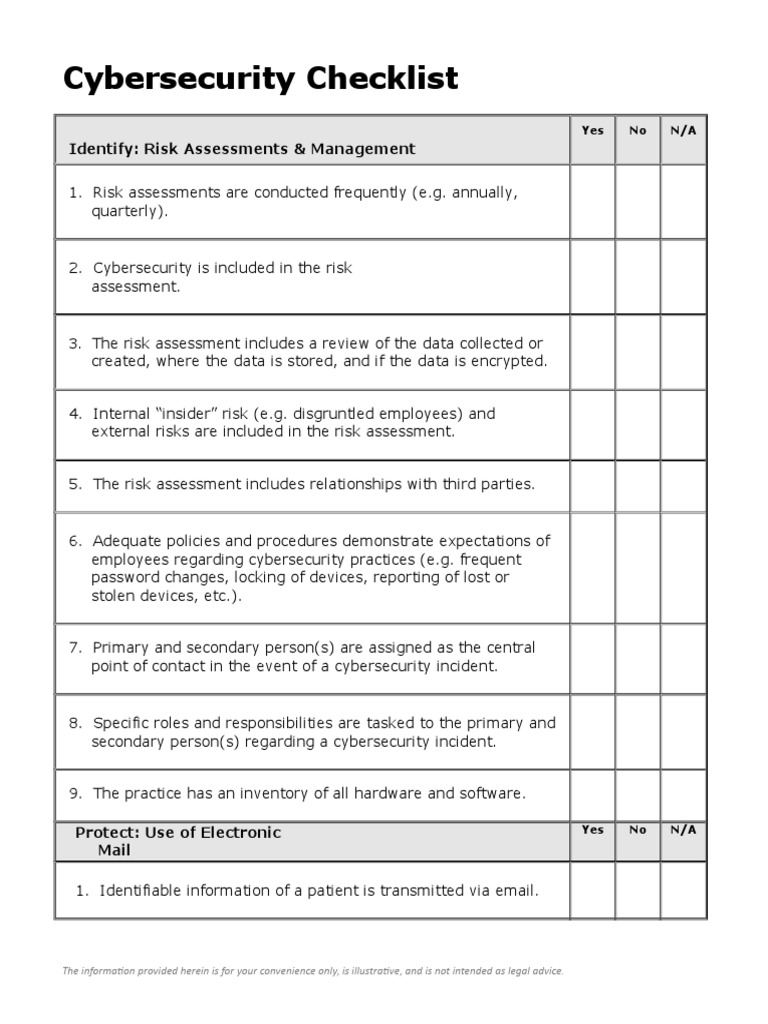
Cybersecurity Checklist Security Computer Security
Just embed the form on your website and start collecting information instantly through a custom job application form. Web sans has developed a set of information security policy templates. Web the us securities and exchange commission ( sec) has adopted new rules requiring publicly listed firms to disclose serious incidents within four days. [today’s date] [hiring manager’s name] 123 company.
Sample Free Sample Security Proposal Security Guards Companies Cyber
Web the cyber security form is a tool used by businesses to protect themselves from online threats. Reread the job description before beginning your cover letter. Personal primary device and data account summary; Used by agencies is securely developed. Web sans has developed a set of information security policy templates.
With Data Breaches Making News, Jobs in Cyber Security on the Rise
Company’s city, state, zip code. Used by agencies is securely developed. Web complete cyber security form online with us legal forms. Suppliers, customers, partners) are established. Just embed the form on your website and start collecting information instantly through a custom job application form.
Nurse Shift Report Sheet Template New National Cyber Ity Incident
Web an online job application form is a website form used to collect information about job candidates. 4 (updated 1/07/22) describes the changes to each control and control. Reread the job description before beginning your cover letter. Web cyber security cover letter template (text format) proper cover letter formatting is essential for making your cover letter look professional and easy.
Used By Agencies Is Securely Developed.
These are free to use and fully customizable to your company's it security practices. Web summary of supplemental files: Check for keywords, skills, certifications and experience the job requires. Whether you’re looking to hire new employees or contractors, use our online job application form to get the job done quickly.
Web Here Are The Steps To Write Your Own Cybersecurity Analyst Cover Letter:
Web the cyber security evaluation tool (cset) download form, which requests the name, email address, organization, infrastructure sector, country, and intended use of those seeking to download the cset. Cybersecurity forms explained and checklist; [today’s date] [hiring manager’s name] 123 company address. Web an online job application form is a website form used to collect information about job candidates.
Add Questions, Change The Background Image, Rearrange Form Fields — Do It All With Our Free Form Builder!
Web the employees then complete the checklist and submit it for review by the senior staff members. Please do not submit actual physical, cyber, emergency response or business continuity plans and do not file this form electronically; Results, or other forms of evaluations to confirm they are meeting their contractual obligations. Web department of homeland security’s cyber safety review board to initiate multiple reviews.
Control Catalog Spreadsheet The Entire Security And Privacy Control Catalog In Spreadsheet Format.
Reread the job description before beginning your cover letter. Personal primary device and data account summary; Ensure that it system managers enforce cybersecurity practices on all business enterprise, process control and communications systems. (1) reduce the likelihood of a damaging cyber intrusion, (2) take steps to quickly detect a potential intrusion, (3) ensure that the organization is prepared to respond if an intrusion occurs, and (4) maximize the organization's resilience to a destructive cyber incident.